Top Cybersecurity Trends Shaping 2026: Stay One Step Ahead of Hackers
Hey, Welcome to the Future of Cyber Defense
Picture this: It’s 2026, and you’re sipping coffee while your smart fridge negotiates with hackers in real-time using AI. Sounds wild? That’s the cybersecurity landscape we’re heading into. As threats evolve faster than ever, staying informed isn’t just smart—it’s survival. In this post, we’ll dive into the hottest trends you need to know about. Buckle up; we’re talking AI showdowns, quantum nightmares, and why “trust no one” is the mantra of the year. Let’s jump in!
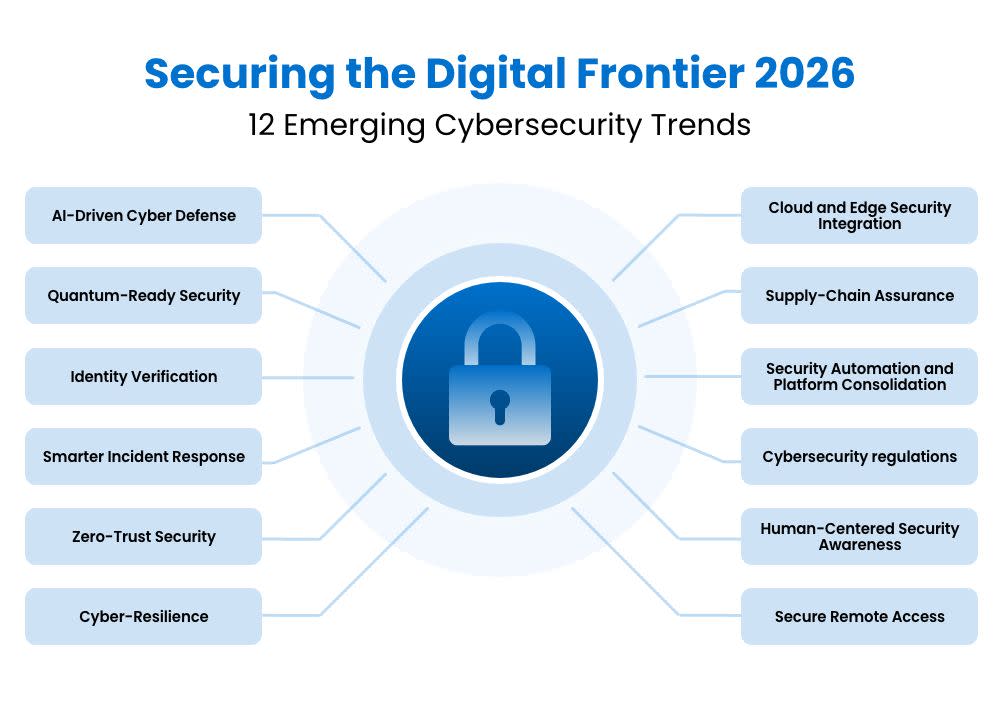
AI: The Double-Edged Sword Taking Center Stage
AI isn’t new, but in 2026, it’s everywhere in cybersecurity—like that overachieving friend who both helps and steals your lunch. On the attack side, cybercriminals are wielding generative AI to craft hyper-personalized phishing emails that mimic your boss’s voice or create deepfake videos for social engineering. Remember those 2025 breaches? They were child’s play compared to AI-orchestrated “swarm attacks” where bots overwhelm defenses in coordinated waves.
But here’s the exciting flip: Defenders are fighting fire with fire. Expect AI-powered “autonomous security operations centers” (AutoSOCs) that predict and neutralize threats before they land. Tools like adaptive machine learning will analyze your network behavior 24/7, spotting anomalies faster than a human ever could. Companies like Palo Alto Networks and CrowdStrike are already prototyping these, and by 2026, they’ll be standard. Pro tip: If your security stack isn’t AI-native yet, time to upgrade—or risk being the next headline.
Quantum Computing: Cracking the Uncrackable
Quantum computers aren’t sci-fi anymore; Google’s and IBM’s beasts are scaling up, promising to shatter today’s encryption like glass. RSA and ECC? Toast by late 2026 if you’re not ready. The big buzz is “post-quantum cryptography” (PQC)—algorithms like lattice-based crypto that quantum machines can’t brute-force.
Governments are mandating PQC migration now, with NIST finalizing standards. You’ll see “harvest now, decrypt later” attacks peaking, where hackers snag encrypted data today for tomorrow’s quantum decrypt. What’s cool? Hybrid systems blending classical and quantum-resistant keys. For businesses, this means auditing crypto everywhere—from VPNs to cloud storage. Ignore it, and your secrets could be public domain faster than you can say “Schrödinger’s breach.”
Zero Trust: No More “Trust, But Verify”—Just Don’t Trust
Zero Trust Architecture (ZTA) went from buzzword to bedrock in 2026. Forget perimeter defenses; every user, device, and app is suspect. Imagine micro-segmentation on steroids: AI verifies identity continuously, context-aware policies block lateral movement, and “least privilege” is enforced via blockchain ledgers.
Why now? Hybrid work exploded, and insider threats (accidental or malicious) spiked 40% last year. Tools like Zscaler’s platform or Microsoft’s Defender are evolving into full ZTA suites with embedded deception tech—fake data traps that lure attackers. For you? Implement continuous authentication on your endpoints. It’s not paranoid; it’s practical. As one CISO told me, “Zero Trust saved my job—twice.”
Ransomware: Smarter, Stealthier, and Subscription-Based
Ransomware isn’t dying; it’s mutating. 2026 sees “RaaS 3.0” (Ransomware-as-a-Service) with subscription models for affiliates, making it accessible to script kiddies worldwide. Attacks now use fileless malware, living off the land with legitimate tools, and double extortion—steal data, encrypt, then dox unless paid.
The trend? AI evasion tactics and targeting critical infrastructure like hospitals and grids. Defenses? Immutable backups, AI anomaly detection, and “breach and attack simulation” tools that red-team your setup monthly. Governments are pushing “no-ransom” policies with international task forces. Bottom line: Backups alone won’t cut it; resilience is key. Train your team—human error still causes 74% of breaches.
Supply Chain Attacks: The Weakest Link Gets Weaker
SolarWinds was a wake-up; 2026 is the reckoning. With global tensions high, nation-states like China and Russia target third-party vendors en masse. Think compromised firmware in routers or open-source libs laced with backdoors. Log4Shell vibes, but automated via AI supply chain scanners gone rogue.
Trends include “software bill of materials” (SBOMs) mandates worldwide and AI-driven vendor risk scoring. Companies like Black Duck are leading with continuous monitoring. For SMBs, join ecosystems like CISA’s shields-up program. Vet your suppliers like they’re family—because one weak link sinks the ship.
Privacy Tech: Zero-Knowledge Proofs Go Mainstream
Privacy isn’t optional; it’s a right. 2026 heralds privacy-enhancing technologies (PETs) like zero-knowledge proofs (ZKPs) in blockchain and apps. Prove you’re over 18 without showing ID? ZKPs make it happen. Homomorphic encryption lets you compute on encrypted data—no decryption needed.
Driven by GDPR 2.0 and U.S. state laws, expect PETs in cloud services (AWS Confidential Computing) and Web3 wallets. It’s huge for health tech and finance. As a user, demand it—tools like Signal are expanding ZKP chats. Cyber pros: Bake privacy into security designs from day one.
IoT and Edge Security: Securing the Exploding Device Army
50 billion IoT devices by 2026? Check. Edge computing decentralizes everything, creating juicy targets. Trends: Matter protocol for smart homes with built-in security, and edge AI for local threat detection. No more phoning home to the cloud.
Botnets like Mirai 2.0 will weaponize unsecured cams and cars. Solutions? Device attestation (proving firmware integrity) and over-the-air updates enforced by law. For enterprises, edge mesh networks with zero trust. Fun fact: Your Tesla might soon self-defend against hacks mid-drive.
Deepfakes and Social Engineering: The Human Firewall Crumbles
Deepfakes aren’t just porn; they’re CEO voice scams costing millions. 2026: Multimodal AI fakes video, audio, even biometrics. Counter? Liveness detection with behavioral AI and watermarking standards from Adobe/Microsoft.
Social engineering evolves to “prompt injection” on AI assistants. Train humans with VR sims—gamified phishing drills. Tools like KnowBe4 are AI-upgraded. Remember: Tech is 50%; people the rest. Foster a “verify everything” culture.
Your 2026 Action Plan: Don’t Get Left Behind
Whew, that’s the 2026 rundown! AI arms race, quantum prep, zero trust forever—these trends demand action. Audit your posture, invest in AI tools, train relentlessly. Cybersecurity isn’t a department; it’s everyone’s job. Stay curious, stay secure. What’s your biggest worry? Drop a comment below!
