5 Alarming Cybersecurity Threats That Will Haunt You in 2024
Picture this: you’re sipping your morning coffee, scrolling through emails on your phone, when bam—a cleverly disguised message tricks you into clicking a link that locks your entire digital life. Sounds like a nightmare? Welcome to 2024’s cybersecurity landscape, where threats are smarter, sneakier, and more relentless than ever. As we dive deeper into an AI-fueled world, hackers aren’t just knocking on your door—they’re picking the lock with tools we barely understand. In this post, we’ll unpack five chilling threats that could haunt your inbox, wallet, and peace of mind this year. Buckle up; knowledge is your best defense.
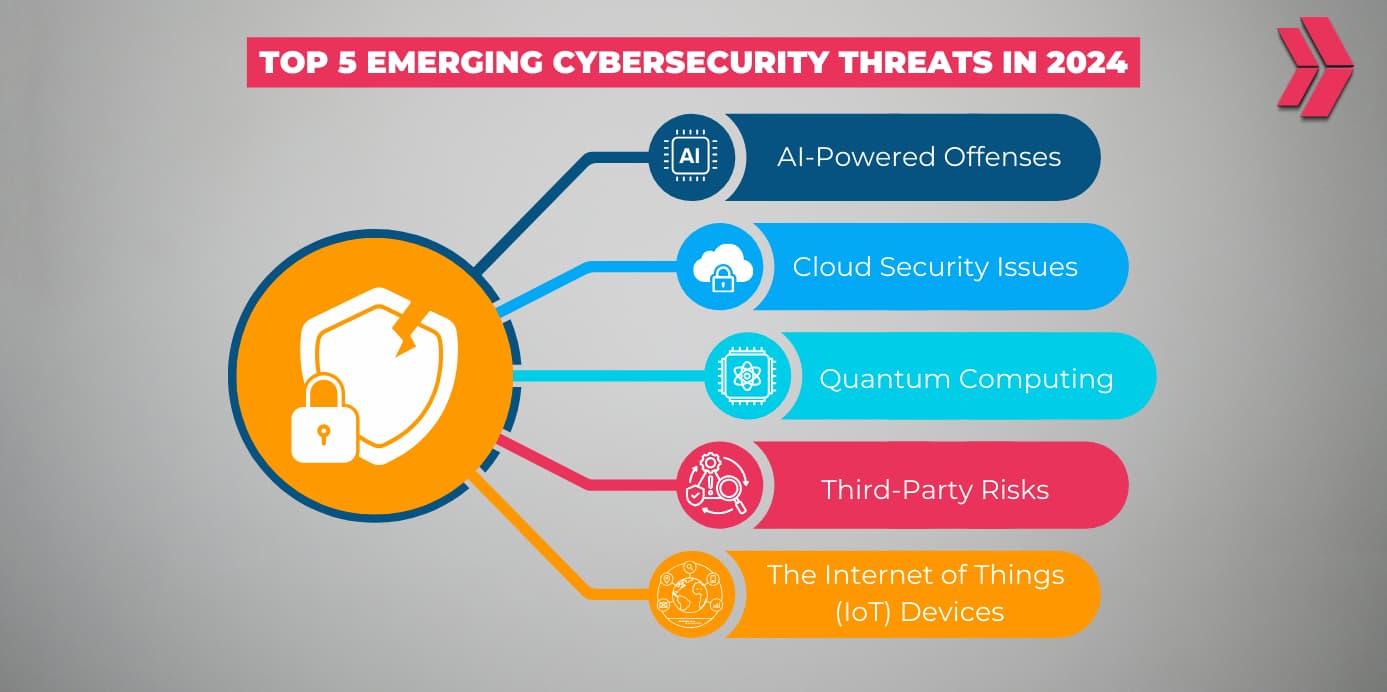
1. AI-Powered Phishing: The Deceptive Mastermind
Remember those clunky phishing emails with bad grammar and shady links? Kiss them goodbye. In 2024, artificial intelligence is supercharging phishing attacks, making them indistinguishable from legit communications. AI tools like advanced language models craft personalized emails that mimic your boss’s tone, your bank’s lingo, or even your spouse’s voice in a voicemail. Tools such as WormGPT and FraudGPT—dark web cousins of ChatGPT—are arming even amateur hackers with pro-level scams.
Why so alarming? A recent report from Proofpoint predicts AI phishing will surge by 300%, targeting not just individuals but entire enterprises. Imagine an email from “HR” with your exact salary details, urging a password reset. Click, and you’re done—credentials harvested in seconds. Real-world scare: Last year, MGM Resorts lost $100 million to a vishing (voice phishing) attack using AI-generated voices. In 2024, expect this on steroids, hitting your smart home devices too.
Don’t panic yet. Fight back by enabling multi-factor authentication (MFA) everywhere, scrutinizing sender domains (hover before clicking), and using AI detectors like those from Google or Microsoft. Stay vigilant—your gut still beats silicon in spotting weird vibes.
2. Ransomware 2.0: Lockbit’s Revenge and RaaS Explosion
Ransomware isn’t new, but 2024’s version is a hydra—cut off one head, two grow back. Groups like LockBit, despite takedowns, are rebounding with Ransomware-as-a-Service (RaaS) models that let script kiddies rent attack kits for pennies. These evolve faster than vaccines, using polymorphic code that mutates to dodge antivirus.
The haunt factor? Double extortion: they encrypt your data and steal it, threatening leaks on dark web sites. Healthcare, schools, and small businesses are prime targets—think hospitals going dark mid-surgery. Cybersecurity Ventures forecasts $265 billion in global ransomware costs by 2031, but 2024 alone could see a 50% spike in attacks per IBM data.
Chilling example: Change Healthcare’s February 2024 breach disrupted U.S. prescriptions nationwide. Protect yourself with regular backups (3-2-1 rule: 3 copies, 2 media, 1 offsite), zero-trust networks, and endpoint detection tools like CrowdStrike. Oh, and patch your software—yesterday.
3. Deepfakes and Social Engineering: Reality’s Evil Twin
Deepfakes aren’t just viral memes anymore; they’re weapons warping trust. In 2024, hyper-realistic video/audio fakes will fuel CEO fraud, where a “boss” video-calls demanding wire transfers, or family emergencies with crying “relatives” begging for crypto. Midjourney and Stable Diffusion make creation child’s play.
Alarming stat: Deepfake incidents rose 550% in 2023 per Sumsub, and 2024 projections from Deloitte warn of nation-state use in disinformation campaigns. Personal horror story: A Hong Kong finance worker lost $25 million to a deepfake video call from his “CFO” in 2024. Your turn? Scammers scrape your social media for voice clones.
Defend with video verification (ask random questions only you know), blockchain-based authenticity tools, and skepticism. Train your team—human error causes 74% of breaches, per Verizon’s DBIR. Question everything that feels off, even if it looks real.
4. Quantum Computing: Cracking Encryption’s Code
Quantum computers are here, and they’re eyeing your encrypted data like a crowbar on a safe. Google’s Sycamore and IBM’s Eagle aren’t sci-fi; they’re breaking RSA and ECC encryption that secures online banking, emails, and state secrets. “Harvest now, decrypt later” attacks are underway—hackers snag your data today for tomorrow’s quantum crack.
Why haunt you? NIST warns 2024 could see first practical quantum breaches, with “Q-Day” looming. Governments are racing to post-quantum cryptography (PQC), but most orgs lag. Your VPN? Toast. Healthcare records? Exposed.
Prep now: Adopt PQC algorithms like Kyber or Dilithium via updates from OpenSSL. Use quantum-resistant VPNs and hardware security modules. It’s not paranoia—it’s future-proofing before the storm hits.
5. Supply Chain Attacks: The Domino Effect
One weak link topples empires. Supply chain hits, like SolarWinds (18k victims) or MOVEit (62M affected), explode in 2024 as attackers target third-party vendors. Open-source libs like Log4j vulnerabilities persist, and nation-states (China, Russia) weaponize them.
Terrifying scale: Mandiant reports a 200% rise in 2023; 2024 brings AI-scanned code for backdoors. Your SaaS provider compromised? Your data’s gone. Small biz owners, you’re not safe—attackers love easy vectors.
Shield up: Vet suppliers with SBOMs (Software Bill of Materials), multi-vendor redundancy, and continuous monitoring. Tools like Wiz or Sysdig scan chains. Assume breach; isolate critical systems.
These threats aren’t distant boogeymen—they’re at your doorstep, evolving daily. But here’s the silver lining: awareness plus action equals armor. Update everything, train relentlessly, and layer defenses. In 2024, cybersecurity isn’t IT’s job—it’s yours. Sleep tighter knowing you’re ahead of the curve. What’s your biggest worry? Drop a comment below!
