The Cyber Hack That Bypassed 2FA on Millions of Devices – Here’s How to Stop It
Picture This: Your 2FA Just Got Useless
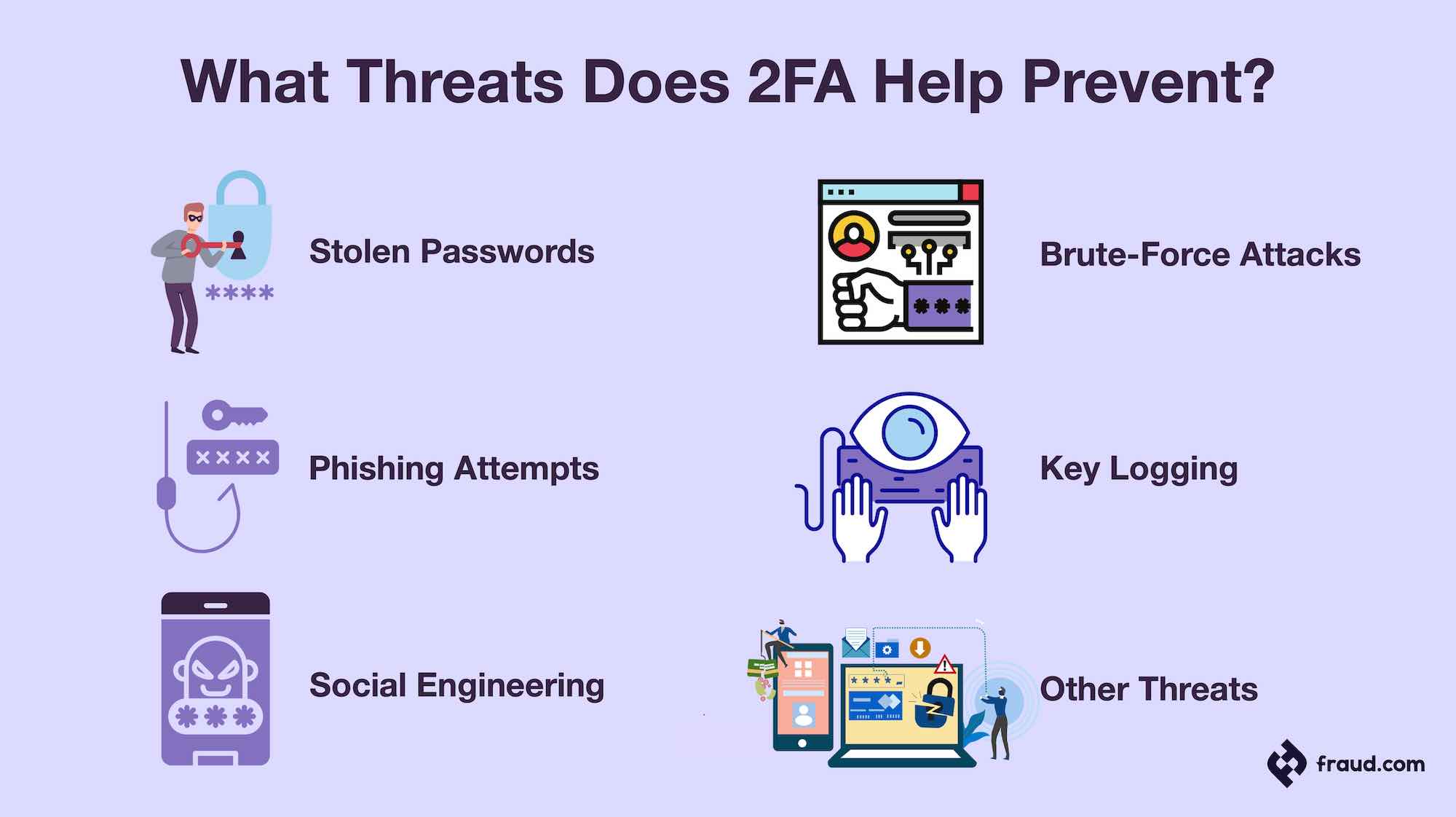
Hey there, tech-savvy friend—or maybe you’re just dipping your toes into the wild world of online security. Either way, buckle up because I’m about to blow your mind with a cyber nightmare that’s already hit millions. We’re talking about a sneaky hack that laughs in the face of two-factor authentication (2FA), the very shield we all thought was bulletproof. Yeah, that pop-up code or SMS you punch in? Hackers are sidestepping it like it’s nothing. And no, this isn’t some sci-fi movie plot—it’s real, it’s happening now, and it could be coming for your accounts next.
Picture logging into your email, your bank, or even your crypto wallet. You get the 2FA prompt, approve it, and think, “I’m safe.” But behind the scenes, cybercriminals have hijacked the whole session. They don’t need your password or your code—they steal the entire login cookie after you authenticate. Boom, they’re in, and you’re out thousands. This is the “EvilProxy” attack (or more broadly, Adversary-in-the-Middle phishing), which has plagued big names like Microsoft, Google, and crypto exchanges. Reports from cybersecurity firms like Netskope and Proofpoint say it’s snagged millions of devices worldwide. Scary? You bet.
How the Hack Actually Works (No PhD Required)
Let’s break it down without the jargon overload—I promise it’ll make sense. Traditional phishing? Hackers trick you into giving your password. 2FA was supposed to stop that because even with the password, they need that second factor. Enter AiTM attacks: hackers set up a fake website that looks identical to the real one (think your bank’s login page).
You type your username and password—bam, they grab it. But here’s the genius evil part: instead of asking for your 2FA themselves (which you’d spot as fishy), they forward you to the real site in a proxy setup. You innocently enter your 2FA code on the legit page, it works, and now the hackers have a valid session cookie. That’s like giving them a master key that bypasses every door from then on. No more codes needed—they’re surfing your account freely.

Why millions? These creeps use massive phishing kits sold on the dark web for pennies. Tools like EvilProxy automate it, targeting high-value spots like Office 365, Amazon, and banking apps. In 2023 alone, attacks spiked 300%, per Zscaler reports. SMS 2FA is the weakest link here—it’s interceptable via SIM swaps or just man-in-the-middle on public Wi-Fi. App-based? Still vulnerable if it’s push notifications, thanks to “MFA fatigue” where you spam approve until you slip.
The Fallout: Real People, Real Pain
This isn’t abstract. Take the 2023 Twilio breach: hackers bypassed 2FA on employee Authy accounts, stealing phone numbers for SMS bombs. Or LastPass in 2022—millions exposed after 2FA fail. Crypto users? Forget it—$100 million+ stolen via session hijacks. Imagine waking up to empty savings, drained IRAs, or ransomware on your work laptop.
One story that chills me: a regular guy in the UK clicked a “bank alert” email. Approved the 2FA push. Next day, £50,000 gone. Companies like Uber and MGM Casinos lost millions in downtime from similar social engineering. Everyday folks? Your Netflix might not hurt, but try losing access to your 401k. Over 163 million records exposed in U.S. breaches last year alone, many tied to 2FA bypasses. It’s not “if”—it’s “when” unless you armor up.
Why 2FA Alone Is Yesterday’s News
We all enabled 2FA thinking it was endgame. Wrong. SMS is trash—carriers admit 30% vulnerability. Push notifications? Hackers fatigue you into “Approve All.” Even TOTP apps (like Google Authenticator) fall to real-time phishing if you’re not careful. The problem? Most 2FA relies on “something you have” that’s still phishable or proxy-able.
Big Tech knows: Apple, Google, Microsoft are pushing passkeys—passwordless magic using biometrics and device-bound keys. But adoption’s slow. Meanwhile, hackers evolve faster than patches. Stats from Okta: 75% of attacks now target post-2FA sessions. Time to level up, folks.
Your Bulletproof Defense: Step-by-Step Guide
Good news—you can stop this cold. No need for a security degree. Follow these, and sleep easy.
1. Ditch SMS 2FA Yesterday. Switch to an authenticator app: Authy, Microsoft Authenticator, or Aegis (Android fave). They generate codes offline—no network snoops. For every account (email, bank, social), regenerate seeds.
2. Go Hardware: YubiKey or Equivalent. These USB/NFC keys ($20-50) use FIDO2 standards. Plug in, tap—hackers can’t phish what they can’t copy. Supports Google, Apple, banks. Pro tip: Get two, one for daily, one backup.
3. Embrace Passkeys Everywhere. Beta on Google/Apple? Enable it. It’s phishing-proof: public-key crypto tied to your device/biometrics. No codes, no cookies to steal.
4. Browser Smarts: Use a Secure One. Brave or Firefox with anti-phishing extensions like uBlock Origin + HTTPS Everywhere. Enable “strict” blocking on Chrome. Never click email links—type URLs manually.
5. Monitor Like a Hawk. Set up login alerts on all accounts. Use Have I Been Pwned? weekly. Tools like 1Password or Bitwarden flag breaches. For work? Push your IT for device compliance.
6. VPN Always on Public Wi-Fi. ExpressVPN or Mullvad encrypts traffic, killing man-in-the-middle. Bonus: ad-blockers stop phishing farms.
7. Train Your Brain. Pause before approving pushes. Weird login location? Deny and investigate. Use a password manager to autofill only on real sites.
Extra Armor: Advanced Tips for Paranoids (Like Me)
Want overkill? Run a Pi-hole at home to block phishing domains network-wide. Enable WebAuthn everywhere it supports. For crypto, hardware wallets + multisig. Audit browser extensions—kill anything sketchy. And FIDO Alliance’s got free resources.
Oh, and update everything. Patches fix proxy vulns weekly. iOS 17+ and Android 14 have built-in AiTM detectors—keep ’em fresh.
Bottom line: This hack preys on trust and speed. Slow down, layer up, and hackers bounce off. I’ve locked down my setup this way—no breaches in years. You can too. Share this if it helped—stay safe out there!
