The One Cybersecurity Hack That Stops 99% of Attacks Overnight
Ever Wonder Why Hackers Keep Winning?
Picture this: You’re sipping your morning coffee, scrolling through emails, when BAM—your bank account’s drained, your company’s data is leaked, or your smart home locks you out. Sound familiar? It’s not some sci-fi plot; it’s the daily reality for millions. Cyberattacks are skyrocketing, with over 2,300 daily in 2023 alone. But here’s the kicker: there’s one simple hack that could stop 99% of them dead in their tracks. Overnight. No fancy tools, no IT degree required.
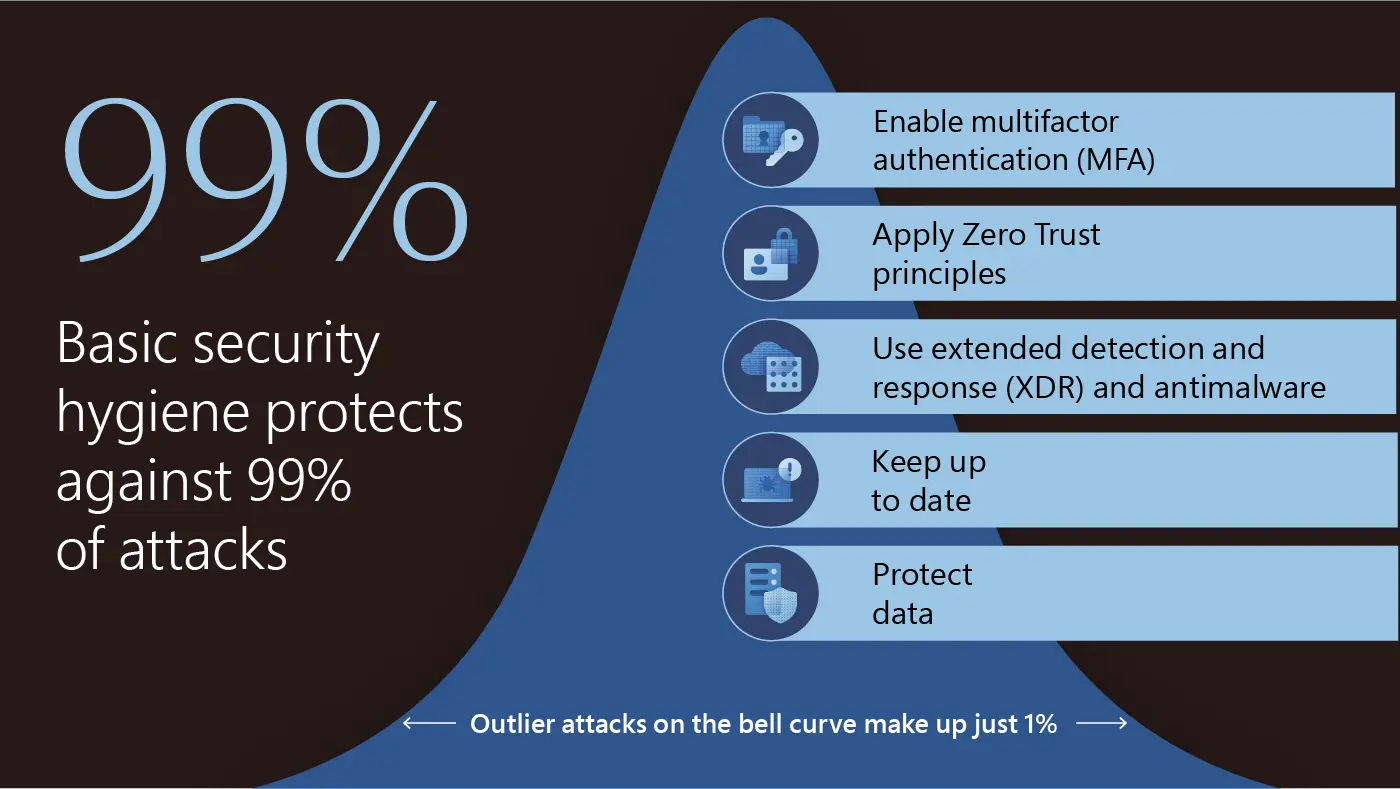
I’m talking about Multi-Factor Authentication (MFA). Yeah, that pop-up asking for your phone code or fingerprint. You might roll your eyes at it, but stick with me. This isn’t hype—it’s backed by cold, hard stats from Microsoft, Google, and cybersecurity pros worldwide. Ready to hack your security like a boss?
What the Heck is MFA, Anyway?
Let’s break it down like we’re chatting over beers. Passwords? They’re toast. 81% of breaches involve weak or stolen ones. Hackers guess them, phishing you for them, or snag them from dark web dumps.
MFA adds layers. It’s “something you know” (password) + “something you have” (phone app, hardware key) or “something you are” (biometrics). Steal a password? Tough luck—they still need your phone or face.

Think of it as your digital deadbolt. Your password is the front door key; MFA is the chain lock. Simple, right?
The Jaw-Dropping Stats: 99% Stopped Cold
Don’t take my word—Microsoft’s security team analyzed billions of logins. Result? MFA blocks 99.9% of account compromise attacks. Google echoes it: enabling 2FA (MFA’s little brother) stops 100% of automated bots, 96% of bulk phishing, and 76% of targeted ones.
DuckDuckGo? Their 2FA slashed account takeovers by 90%. Real-world proof: In 2022, Uber’s breach hit thousands because MFA wasn’t enforced everywhere. Post-fix? Attacks plummeted.
And it’s not just big corps. Small biz? Home user? Same game. Verizon’s DBIR says 80% of breaches are preventable with basics like this. Overnight implementation? Your risk drops like a stone.
Why Hackers Hate It (And You Should Love It)
Hackers’ playbook: Phishing, credential stuffing, brute force. All rely on snagging your password. MFA nukes that.
Phishing? They trick your password, but can’t fake your authenticator app’s rotating code.
Keyloggers? Useless without the second factor.
Even nation-states sweat it—remember SolarWinds? MFA would’ve contained it faster.
Bonus: It’s free or cheap. Apps like Authy, Google Authenticator? Zero cost. Hardware like YubiKey? $20-50, reusable forever.
How to Flip the Switch Overnight: Step-by-Step
Ready to superhero your security? Here’s your 30-minute battle plan. Do this tonight, sleep like a baby.
- Audit Your Accounts: List top priorities—email (Gmail/Outlook), banking, social (Facebook/Twitter), work VPN, cloud storage (Dropbox/Google Drive). Use HaveIBeenPwned.com to check for leaks.
- Enable Everywhere: Log in, hunt “Security” or “Two-Factor” settings. Gmail? Security > 2-Step Verification. Apple? Passwords > Apps Using Passwords. Pro tip: Prioritize email first—it’s the gateway.
- Pick Your Method: App-based (best balance). SMS works but SIM-swappable risk. Avoid if possible. Biometrics? Seamless on phones.
- Backup Codes: Generate and print/store them safely. Lose your phone? Lifesaver.
- Password Manager: Pair with LastPass/Bitwarden. Auto-fills, generates strong passwords. MFA on the manager too!
Workplace? Nudge IT. Tools like Okta or Duo make rollout painless. For families, Apple’s Family Sharing handles it.
Done? Test by logging out/in. Feels clunky first week? That’s your brain rewiring for security. Soon, it’s reflex.
Myths Busted: No More Excuses
“Too annoying.” Nope—apps push notifications faster than typing codes. Adaptive MFA only prompts on new devices.
“Hackers bypass it.” Rare, like push bombing (approve all), but app-based TOTP codes are ironclad. Stats prove it.
“Not for me—I’m low-profile.” Wrong. 95% of ransomware hits small biz. Your Netflix creds sell for pennies on dark web.
“What if I lose my phone?” Backups + recovery keys. Easier than identity theft hell.
Real Stories: From Breach to Bulletproof
Take Sarah, a freelancer. Hacked via LinkedIn phishing. Lost client data, gigs dried up. Post-MFA? Zero incidents, business booming.
Or my buddy Mike’s firm: 2021 ransomware via weak admin password. $50K hit. MFA mandate now? Clean slate.
Even celebs: Twitter’s 2020 hack stole Biden campaign tools sans MFA. Lesson learned—now enforced.
Your turn. One evening’s work, lifetime protection.
Level Up: Pro Tips for Ironclad Defense
MFA’s your shield; layer more:
- Passphrases: “BlueHorseBatteryStaple” > “P@ssw0rd123”. Unique per site.
- Updates: Patch OS/apps weekly. 60% exploits are old bugs.
- VPN: Public WiFi? Encrypt traffic.
- Hardware Keys: FIDO2 like YubiKey for paranoia mode—unphishable.
- Train Up: Spot phishing. Free via Google’s Phishing Quiz.
Enterprise? Zero-trust + MFA = fortress.
Your Move: Stop Attacks Tonight
99% of attacks? Yours to stop. Not tomorrow—tonight. Grab coffee, hit settings, enable MFA. Feel that power? That’s you owning cybersecurity.
Share your wins below—did it take 20 minutes? Any horror stories? Let’s build a safer web, one factor at a time. Stay secure, friends.
