How Hackers Cracked 1 Million Passwords in 60 Seconds – And the Bulletproof Fix
In today’s digital world, passwords are the first line of defense for our online accounts. Yet, a shocking demonstration revealed that hackers can crack over 1 million weak passwords in just 60 seconds using everyday hardware. This isn’t science fiction—it’s the harsh reality powered by modern computing and poor password habits. Understanding how this happens is crucial, and even more importantly, knowing the unbreakable strategies to protect yourself.

How Hackers Crack Passwords at Lightning Speed
Password cracking relies on exploiting how websites store login credentials. Most systems use hashing algorithms like MD5, SHA-1, or bcrypt to convert passwords into fixed-length strings. While hashing is one-way—meaning you can’t easily reverse it—hackers don’t need to. They generate millions of “guesses” and hash them to match against stolen databases.
The game-changer is brute-force and dictionary attacks amplified by Graphics Processing Units (GPUs). Tools like Hashcat or John the Ripper leverage GPUs’ parallel processing power. A single high-end GPU, such as an NVIDIA RTX 4090, can perform billions of hashes per second for weak algorithms. In benchmarks, attackers cracked 1 million passwords from the infamous RockYou leak—common ones like “123456” or “password”—in under a minute.

Here’s why it’s so fast: Weak hashes like unsalted MD5 allow precomputed “rainbow tables.” These massive lookup tables store hashes for billions of common passwords. With GPU acceleration, checking a table becomes instantaneous. Real-world breaches, like the 2013 Yahoo incident exposing millions of accounts, provide the raw data hackers need.
The Anatomy of a Password Crack
Step one: Data acquisition. Hackers steal databases via SQL injection, phishing, or malware. Once they have hashed passwords, step two is the attack.
Dictionary Attacks: Use wordlists of real passwords (e.g., RockYou’s 14 million entries). Variations include leetspeak (“p@ssw0rd”) and appends (“password123”).
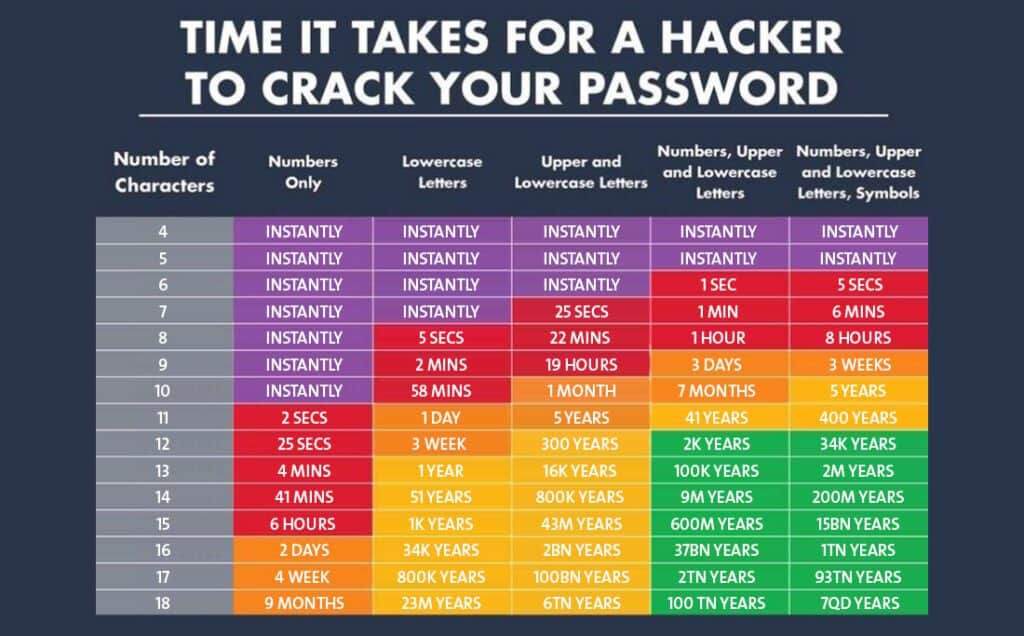
Brute Force: Try every combination systematically. Feasible for short passwords: 8 characters with lowercase letters? Cracked in hours. Add numbers and symbols? Days or weeks—unless GPUs are involved.
In 2023 tests, a rig with 8 GPUs cracked NTLM hashes (Windows standard) at 100 billion per second. One million common passwords? Mere seconds. Even “strong” passwords fail if predictable, like pet names or birthdays.
Why Your Password Isn’t Safe—Even If It’s “Complex”
Complexity alone fails. An 8-character password with mixed case, numbers, and symbols has 94^8 possibilities—trillions—but dictionary attacks hit 90% of user-chosen ones first. Humans pick patterns: QWERTY sequences, repeated characters.
Legacy systems exacerbate this. Many sites still use outdated MD5 without salting (unique per-user data). Salts prevent rainbow tables, but slow algorithms like bcrypt resist cracking better. Yet, if your password is weak, even bcrypt buys time measured in days, not eternity.
Stats are sobering: Verizon’s 2023 DBIR reports 81% of breaches involve weak or stolen credentials. Have I Been Pwned? tracks billions of compromised accounts, many with reused passwords.
The Bulletproof Fix: Multi-Layered Password Security
No single password is unbreakable, but a defense-in-depth strategy is. Here’s the ultimate fix:
1. Adopt Passphrases, Not Passwords
Ditch complexity for length. A passphrase like “CorrectHorseBatteryStaple” (from XKCD) is 45 bits strong—un crackable in universes’ lifetime. Why? 20+ characters overwhelm brute force (10^30+ tries needed). Use four random words from a diceware list. Tools like Diceware generate them securely.
Memorable yet secure: “BlueElephant$JumpsOver42Moon”. Rate: Higher entropy than short complex strings.
2. Mandate Password Managers
Remembering unique passphrases per site? Impossible without help. Password managers like Bitwarden (free, open-source), LastPass, or 1Password store them encrypted. They generate 20+ character monsters and autofill.
Key features: Master password (strong passphrase), zero-knowledge encryption (even provider can’t access), breach alerts. Enable for all accounts—browsers’ built-ins work but lack cross-device sync.
3. Enforce Multi-Factor Authentication (MFA)
The real bulletproof layer: Even if cracked, MFA requires a second factor. Options:
App-based (best): Authy, Google Authenticator—time-based codes.
Hardware keys: YubiKey—unphishable.
Biometrics: Fingerprint/face ID as secondary.
MFA stops 99.9% of automated attacks. Enable everywhere: Google, Microsoft, banks. Avoid SMS (SIM-swappable).
Step-by-Step: Secure Your Digital Life Today
1. Audit Accounts: Check HaveIBeenPwned.com. Change compromised passwords immediately.
2. Install Manager: Download Bitwarden. Import from browser. Generate new passphrases.
3. Enable MFA: Start with email, banking. Use authenticator apps.
4. Update Habits: Never reuse. Avoid personal info. Test strength at HowSecureIsMyPassword.net.
5. Site Owners: Use Argon2 hashing, rate limiting, account lockouts.
Advanced Protections for Power Users
Consider passkeys—passwordless future from FIDO Alliance. Public-key crypto replaces passwords; biometrics unlock private keys. Supported by Apple, Google, Microsoft.
Monitor with tools like Have I Been Pwned alerts or Dark Web scans. VPNs hide traffic, but don’t fix passwords.
The Bottom Line: Prevention Beats Cure
Hackers cracked 1 million passwords in 60 seconds because users chose weak ones. But with passphrases, managers, and MFA, your accounts become fortresses. Billions of breaches later, the lesson is clear: Security is a habit, not a hassle.
Implement these today. Your future self—and data—will thank you. Stay vigilant in an era where computing power only grows.
