Why Your Current Password Strategy is Leaving You Vulnerable
In today’s digital age, passwords are the frontline defense against cyber threats. Yet, despite their critical role, most people’s password strategies are woefully inadequate. According to Verizon’s 2023 Data Breach Investigations Report, 81% of breaches involved weak or stolen credentials. If you’re still using simple passwords like “password123” or recycling the same one across multiple sites, your current password strategy is leaving you vulnerable. This article explores why common practices fail, the dangers they pose, and how to fortify your defenses for better online security.
Common Flaws in Traditional Password Strategies
Feature Video
Many users cling to outdated password habits that cybercriminals exploit effortlessly. The first major issue is password reuse. A study by Google found that 65% of people reuse passwords across accounts. When one site gets breached—as happens frequently with major platforms like LinkedIn or Yahoo—hackers gain access to your email, banking, and social media with minimal effort. Your “convenient” strategy becomes a hacker’s roadmap.
Weak passwords compound this problem. Have I Been Pwned? database reveals billions of compromised credentials, with top offenders including “123456,” “qwerty,” and “password.” These are cracked in seconds using dictionary attacks or brute-force tools. Even slightly better ones like “FluffyDog2023” fall if predictable patterns emerge. Without complexity—uppercase, lowercase, numbers, symbols—and sufficient length (at least 12-16 characters), your password strategy lacks resilience.
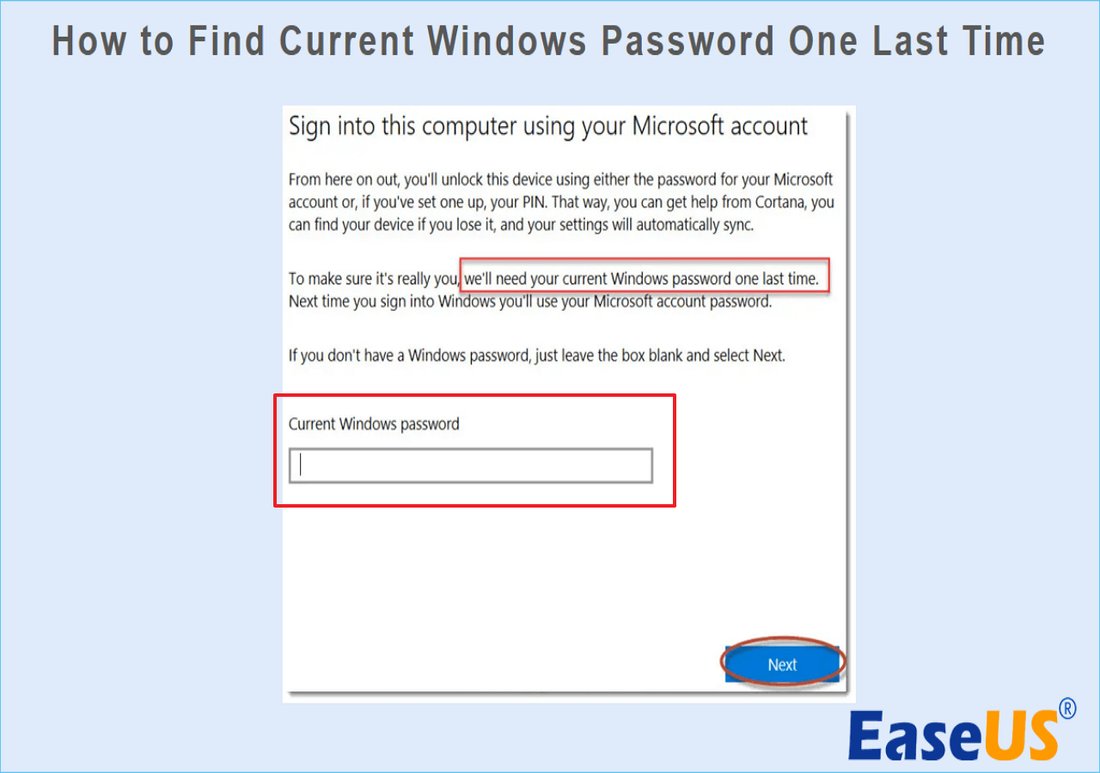
Another pitfall: ignoring password managers. People memorize a handful of passwords and default to weak ones elsewhere. Manual tracking leads to notes on phones or sticky notes under keyboards—prime targets for physical theft or remote access. Without a manager like LastPass or Bitwarden, generating and storing unique, complex passwords is impractical, perpetuating vulnerability.
Sharing passwords with family or friends seems harmless but opens backdoors. Once shared, control is lost. A trusted contact’s device compromise or careless behavior exposes you. Surveys show 40% of users admit to sharing, undermining even strong individual practices.
The Devastating Risks of Inadequate Password Protection

Poor password strategies invite severe consequences. Data breaches are rampant; in 2023 alone, over 3,200 breaches exposed 353 million records, per Identity Theft Resource Center. Stolen credentials enable account takeovers, where hackers drain funds, steal personal data, or launch ransomware.
Identity theft follows closely. With email access, attackers reset passwords on financial sites, racking up debt in your name. The FBI’s 2022 Internet Crime Report noted $10.3 billion in losses from cybercrimes, many stemming from credential stuffing—automated attacks using breached logins.
Financial repercussions are direct. Banking apps breached via weak passwords lead to unauthorized transactions. Businesses suffer too; employee credential compromise costs firms an average $4.45 million per breach, says IBM. Individuals face credit damage, legal fees, and endless recovery hassles.
Beyond finances, privacy erosion occurs. Social media hacks spread misinformation or dox you. Corporate espionage via executive logins disrupts operations. Your current password strategy isn’t just risky—it’s a ticking time bomb in an era of sophisticated phishing like credential harvesters disguised as login pages.
Why Multi-Factor Authentication (MFA) Alone Isn’t Sufficient
MFA adds a second verification layer, like a texted code or app push. It’s better than passwords alone—Microsoft blocks 99.9% of attacks with it. However, relying solely on MFA with weak passwords remains vulnerable. SIM-swapping bypasses SMS codes; 911 calls reroute via hijacked numbers. App-based MFA can be phished via man-in-the-middle attacks.
Even hardware keys like YubiKey aren’t foolproof without strong base passwords. NIST guidelines emphasize passwords as the foundation—MFA enhances, doesn’t replace. If your password is “password1,” MFA delays but doesn’t stop determined foes. A holistic strategy integrates both.
Real-World Examples of Password Failures
High-profile breaches underscore the point. The 2021 Colonial Pipeline hack started with a single compromised VPN password, halting U.S. fuel supplies. Equifax’s 2017 breach, from unpatched software and poor credential hygiene, exposed 147 million records, leading to $700 million in settlements.
Everyday users suffer too. In the 2023 MOVEit breach, weak supply-chain passwords cascaded to millions. Personal stories abound: a Reddit user lost $20,000 after password reuse; another endured identity theft from a shared family login. These aren’t anomalies—your strategy mirrors theirs.
Building a Bulletproof Password Strategy
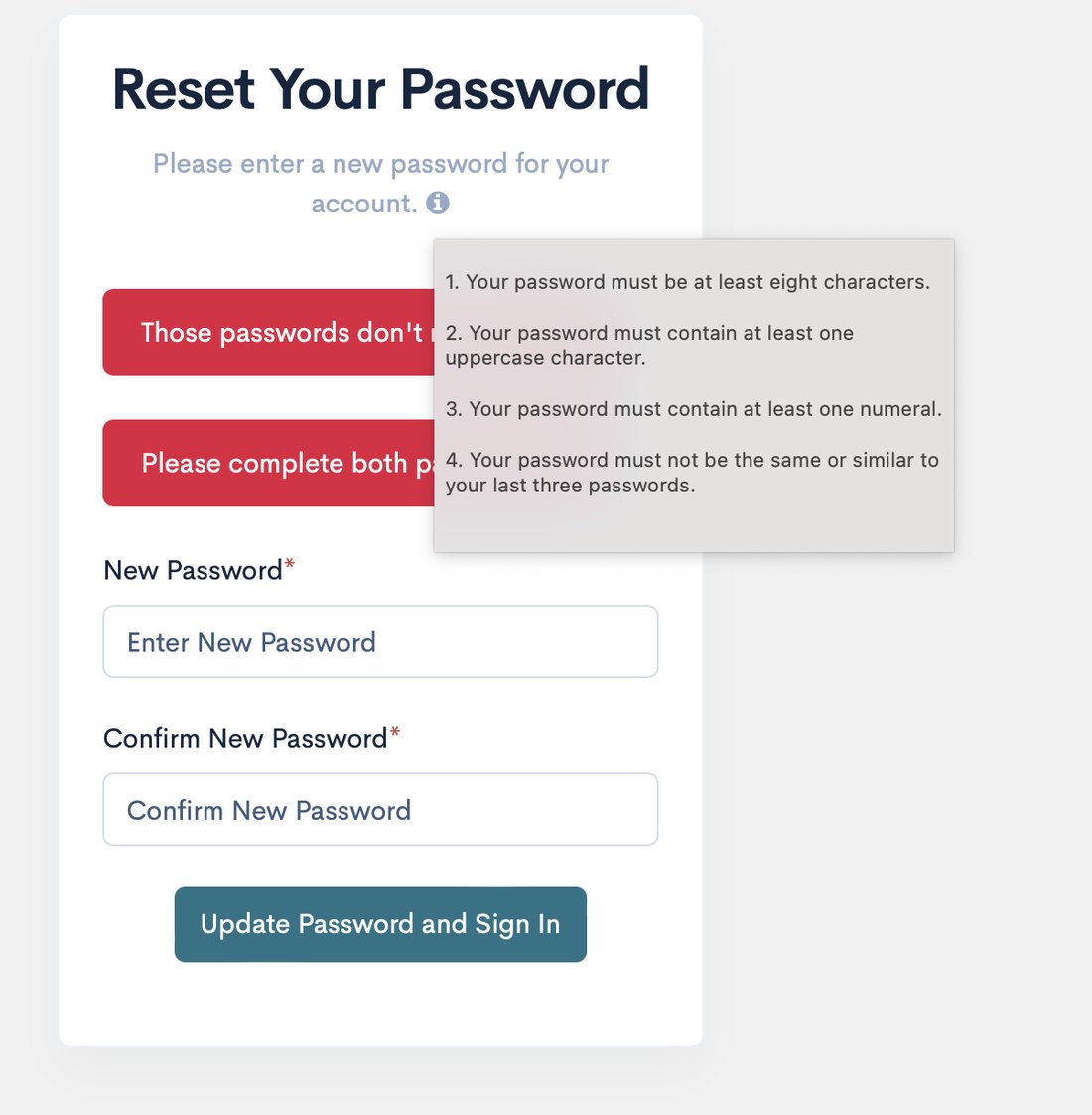
Revamp starts with passphrases: memorable strings like “CorrectHorseBatteryStaple” (from XKCD) resist cracking better than jumbled characters. Aim for 20+ characters; they’re exponentially harder to brute-force.
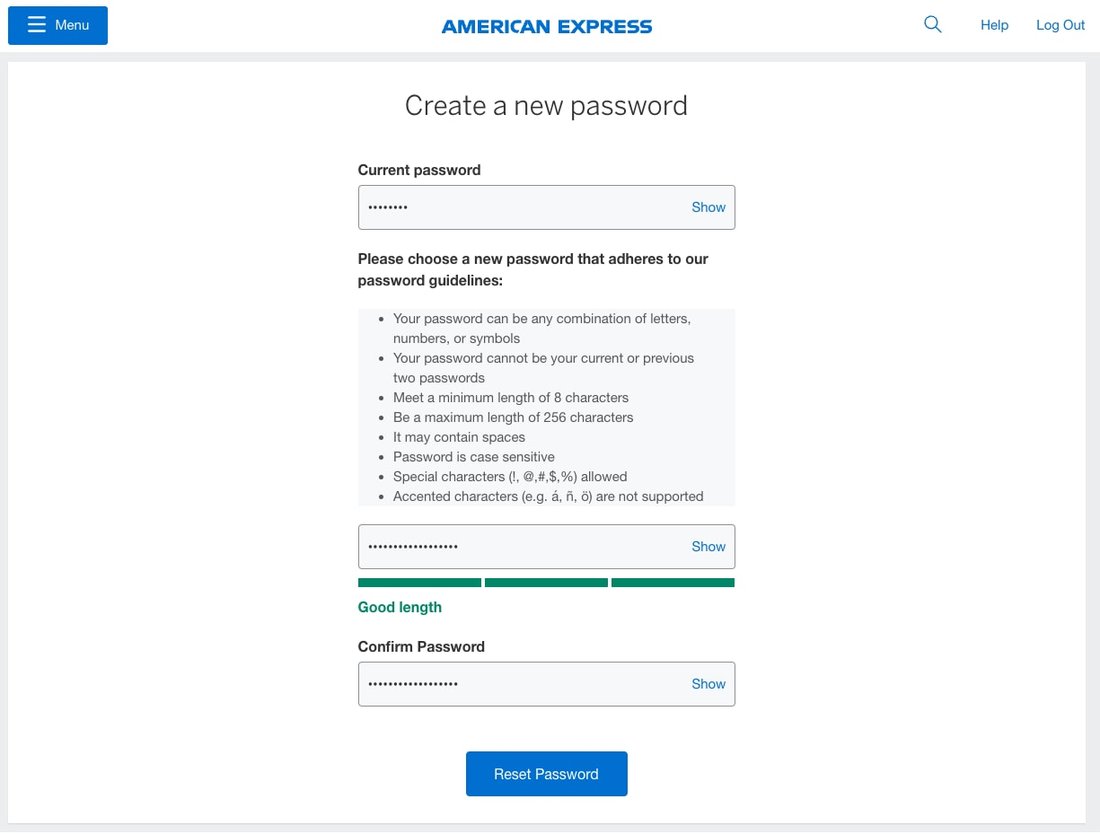
Adopt a password manager. Tools like 1Password or Dashlane generate, store, and autofill unique passwords per site. Encrypted vaults sync across devices with master password + MFA protection. Free options like Bitwarden suffice for most.
Enable MFA everywhere, prioritizing app-based (Google Authenticator) or hardware over SMS. Biometrics (fingerprint/face ID) add convenience but pair with strong backends.
Regular audits are key. Use Have I Been Pwned? to check exposures; change affected passwords immediately. Browser extensions like Password Checkup flag weaknesses. Avoid periodic changes unless breached—frequent swaps encourage simplification.
For businesses, enforce policies: minimum lengths, no reuse, manager mandates. Train on phishing recognition; 36% of breaches involve social engineering.
Emerging Threats and Future-Proofing Your Approach
Quantum computing looms, potentially shattering current encryption. Post-quantum cryptography is developing, but strong passwords buy time. AI-driven attacks personalize phishing, guessing patterns from social media.
Passkeys—passwordless tech from FIDO Alliance—emerge as successors. Using public-key crypto, they’re phishing-resistant. Apple, Google, Microsoft support them; transition soon.
Zero-trust models assume breach, verifying continuously. Individuals mimic via device encryption, VPNs, and minimal data sharing.
Conclusion: Secure Your Digital Life Today

Your current password strategy is leaving you vulnerable because it prioritizes convenience over security in a threat-laden world. Common mistakes like reuse and weakness, amplified by breaches and phishing, expose you to identity theft, financial ruin, and privacy loss. Shift to passphrases, managers, MFA, and vigilance. Tools are accessible; excuses aren’t.
Act now: audit accounts, install a manager, enable MFA. In cybersecurity, vigilance is survival. A robust password strategy isn’t optional—it’s essential for safeguarding your digital identity.
(Word count: 1,248)
